How Biometric Systems Work (A non-technical primer)
 We recently published a white paper that describes how biometric devices are transforming online, mobile, ATM and in-branch banking. It discusses the common challenges banks face when they deploy solutions and how biometric solutions benefit banks and their customers. The white paper assumes the reader already understands the fundamentals of how biometric systems work and the options that are currently available. This blog series is written for those who would like a quick introduction to a similar foundation.
We recently published a white paper that describes how biometric devices are transforming online, mobile, ATM and in-branch banking. It discusses the common challenges banks face when they deploy solutions and how biometric solutions benefit banks and their customers. The white paper assumes the reader already understands the fundamentals of how biometric systems work and the options that are currently available. This blog series is written for those who would like a quick introduction to a similar foundation.
What Is Biometric Identification?
Biometric devices automatically identify a person based on physical or behavioral characteristics. Generally, such traits do not change over time so the biometric data associated with those traits can be used to authenticate an individual throughout his or her lifetime.
How Biometric Authentication Works
Biometric devices consist of three components: a reader/scanner, software that converts the capture information into digital form, and a database that stores the biometric data so it can be compared to the previous record associated with an individual.
The software is responsible for processing the information. It identifies specific points of data as “match points.” The match points are processed into a value using an algorithm and then the value is compared with the data stored in the database.
Biometric solutions use a two-step authentication process that consists of enrollment and verification.
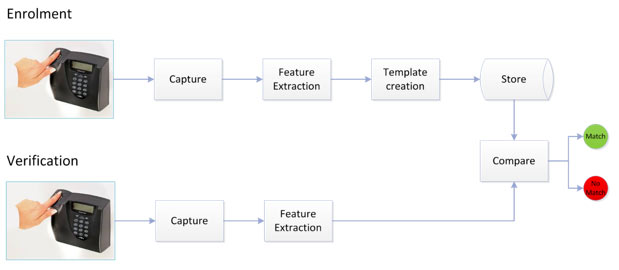
How Enrollment Works
Enrollment has three steps:
- Capture – The system captures a user’s physical or behavioral trait, such as a fingerprint or signature.
- Feature Extraction – The software enhances the input from the sensor, removing the noise and unwanted elements to achieve the desired format for efficient feature extraction. Distinctive and repeatable features are selected.
- Template Creation and Store – The cleansed and enhanced user data is stored in the feature template, which is stored in a database for later retrieval. Unwanted elements are removed to reduce the template’s size. The template is then used for matching in the future.
How Verification Works
During Verification, a sensor captures the biometric trait for which it was designed. An algorithm analyzes the trait and then a matcher compares the trait to an existing template in the Enrollment database. This stage consists of two steps:
- Comparison/Classification – The biometric data is compared with the stored template.
- Decision Making – The system decides whether the new data is a match or a non-match based on a threshold match score.
The threshold match score is important. While it allows for slight variations, such as in a person’s tone of voice or signature, such variations much fall within a certain range. If the score exceeds the threshold score, it is not considered a fit. The system automatically flags the suspicious activity and generates management reports.
The Benefits and Challenges of Biometric Authentication
Biometric devices allow banks to more quickly and easily identify customers and employees. Fingerprints, hand geometry, facial geometry, irises, retinas, voice patterns, and signature patterns are far more difficult to falsify than Personal Identification Numbers (PINs) or passwords (which anyone without technical knowledge can exploit) and tokens (which can be compromised by advanced, tech-savvy users).
Like any other method of identification, biometric solutions are not absolutely secure (which I discuss more in the second blog in this series). However, they can provide more robust levels of security than traditional authentication solutions, particularly when implemented properly.
The white paper explains many important issues banks should consider when implementing biometric solutions. It also explains why biometric solutions are gaining momentum quickly.
If you want to find out what options are available and which countries are adopting them, please read part 2 of this series. In the meantime, if your bank is currently using biometric devices or if you have questions, please leave a comment below.